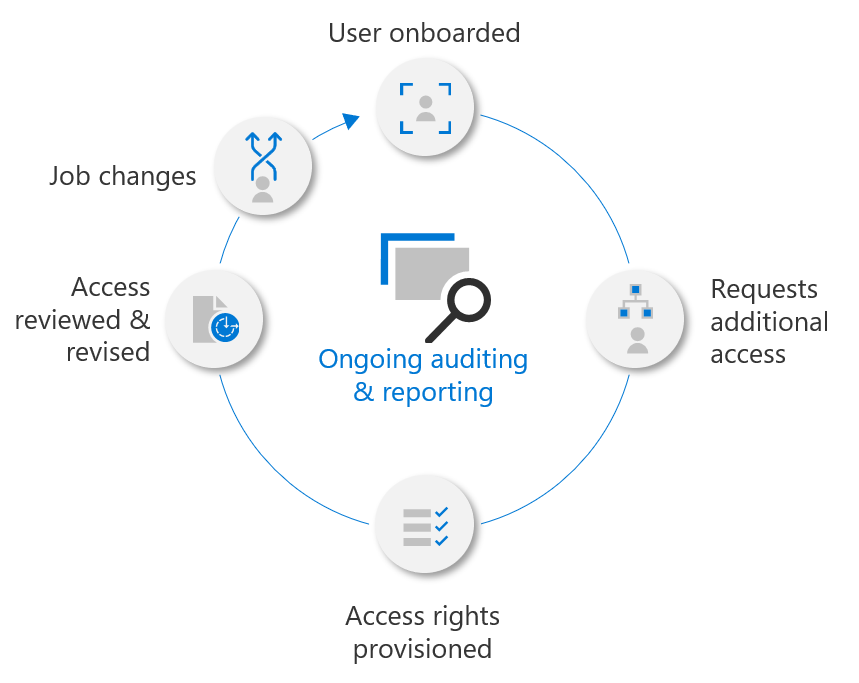
Entitlement Management in Azure AD allows organizations to automate access request workflows, access assignments, reviews and expiration. When an employee needs permissions or access to a tool or program, it might be difficult to identify the specific person in the organization that can approve the access (especially in larger organizations). A great example is Microsoft Visio, Microsoft Project or any other licensed software. Since these applications require additional licenses, the organization can save costs by only providing licenses to those employees that have a business justification. Additionally removing licenses for those users who no longer require the products is equally important.
In this post we will use Entitlement Management to create Access Packages for Microsoft Visio so that any user in our organization can easily request the application. Endpoint Manager will automatically publish the software to approved users through Company Portal. Finally we will use Access Reviews to audit and review access, removing access to those who no longer have a valid business justification. Of course this is just an example, Access Packages and Access Reviews can be used for a large variety of things and this is just one use-case of many. By utilizing these tools our identity lifecycle becomes easier to manage and we have more insights and control.
Contents
- What is Entitlement Management
- Requirements
- Creating an Access Package
- Requesting an Access Package
- Creating an Access Review
- Preforming an Access Review
What is Entitlement Management
Gartner defines Entitlement management as “technology that grants, resolves, enforces, revokes and administers fine-grained access entitlements”. In terms of Azure AD identity governance this means Access Packages and Access Reviews.
Access Packages
Access Packages allow users to request access to a single or group of resources such as a Group, Application, Team or SharePoint Site. Access Packages are especially great when dealing with time-limited access, such as a consultant that needs access to a specific set of resources or privileges to do a specific task. Most organizations have restricted areas or groups that only certain people in management or those with a specific role or function can access. For example a SharePoint site containing corporate secrets or HR data that should be restricted to specific individuals. All these examples and many more are perfect use-cases for Access Packages.
Access Reviews
Access Reviews allows administrators or those that have been delegated to review who has access to a specific set of resources. These can be scheduled at intervals or manually triggered to make sure only those individuals with a specific business justification have access to restricted resources. For example a person who previously worked in HR might retain their access to sensitive information after starting a new position that does not require access. Using Access Reviews would uncover that the user still had access, and the reviewer could easily resolve the issue.
Most organizations have applications and/or service owners for the products and services used within the organization. Delegating tasks such as access governance to the service owner rather than having IT perform such tasks is not only more efficient but also allows IT personell to focus on other tasks. If Access Packages are used throughout the organization, the My Access portal becomes a one-stop shop that allows for self-service and provides a great workflow for end-users.
Requirements
Entitlement Management is part of the Azure AD Premium 2 license, which is available as a stand-alone license or in the Microsoft 365 E5 and Enterprise Mobility + Security E5 (EMS) packages.
Microsoft is known for having complex licensing and Entitlement Management is no exception. Licenses must be assigned to all users (members) who can request an access package, regardless if they use an access package or not. As long as a regular user has an access package available they must be licensed. Although no license is required to create access reviews and access packages, any user who will be approving or reviewing requests and assignments will need a license. Licensing is also a little different for guest users. A guest user only needs a license if they actually request an access package or will be approving / reviewing requests and assignments. See Microsoft’s licensing documentation for more information.
Creating an Access Package
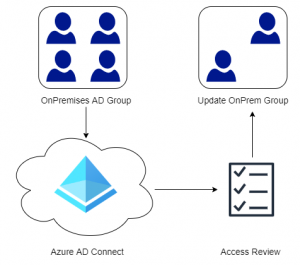
Prior to creating the Access Package an empty Azure AD Security Groups called License Group – Microsoft Visio was created. Visio Licenses have been assigned to the group so that any user who is added to the group is provided a license. Optionally create a Visio applications in Endpoint Manager and publish it to the same group. This will allow our end-users to easily install the software from Company Portal once access has been approved.
Tip: If you are creating an Access Package for an application like Dropbox or Salesforce, consider integrating Azure AD with these applications. Then use the Provisioning functionality in Azure AD to automatically provision the users. See my blog post on Integrate Third-Party Applications with Azure AD.
- In the Azure Portal open Azure Active Directory and select the Identity Governance blade.
- Select Access Packages from the left-hand side then click New Access Packages.
- On the Basics page, give the Access Package a Name and a Description. A new Catalog can be created to group similar access packages together or simply use the General catalog.
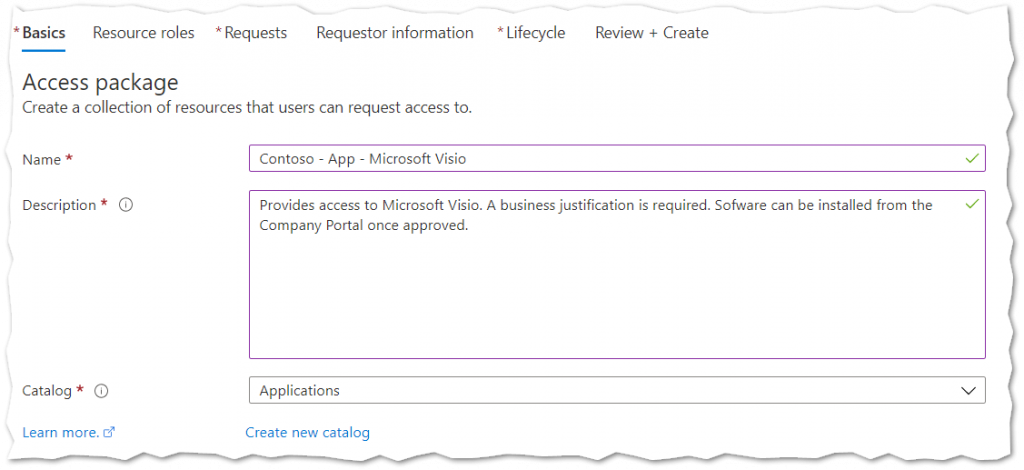
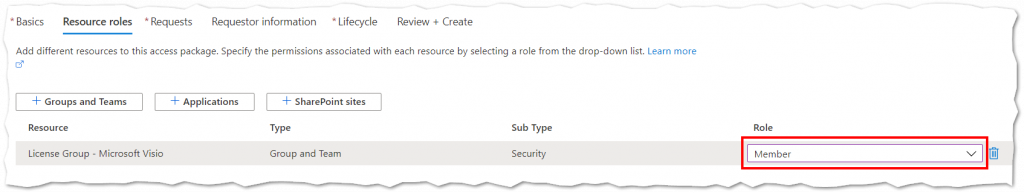
- On the Resource Roles page, select Groups and Teams. Select the license group for Visio. Only groups that have been previously used with the specific Catalog are displayed. To add a new group select See all Group and Team(s) not in the ‘Applications’ catalog checkbox.
- Once a group has been chosen, make sure to select if a user should be added as Member or Owner when the Access Package is requested.
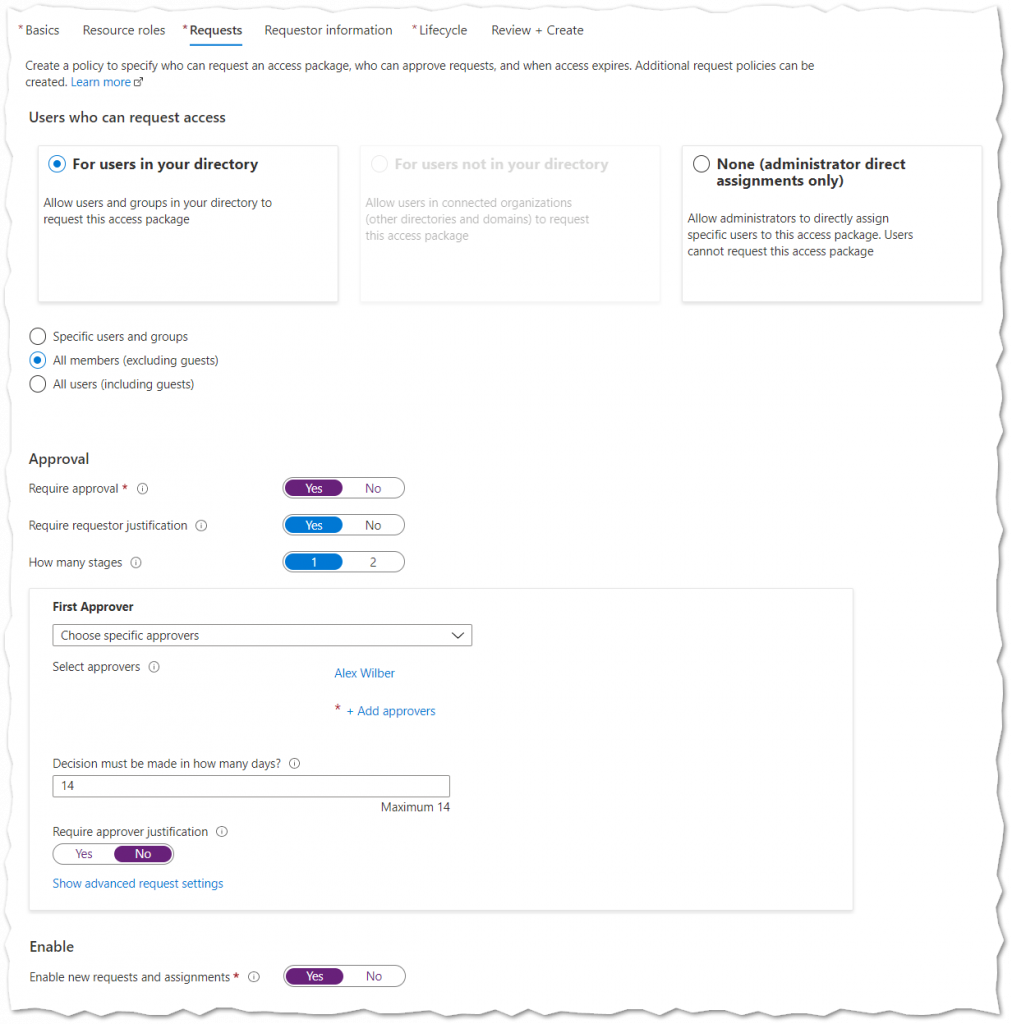
- On the Requests page, select who should be able to request the Access Package and if Approval is required.
In our case we only want our internal users to be able to request the access package. Any users who request the access package need to specify a business justification and we will require approval.
- On the Requestor Information page specify any additional mandatory or optional questions that the requestor should complete when requesting the Access Package. Examples could be department, customer or invoice code. In our example we will leave this blank as justification has already been enabled in the previous step and we wont require additional information from the user.
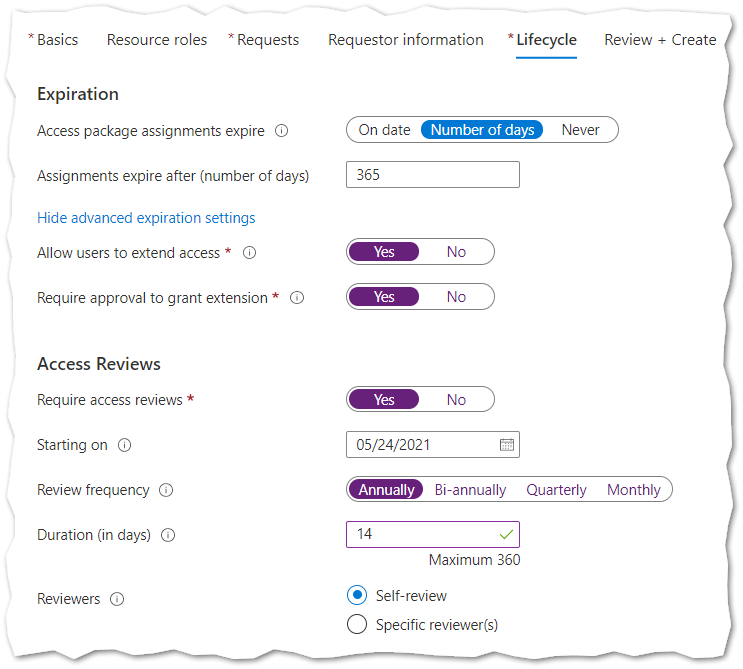
- Finally on the Lifecycle page, choose if the Access Package should expire or not, and if Access Reviews are required. Complete the wizard and create the Access Package.
In our example we have set our Access Package to expire after 1 year (365 days). User are able to extend their access for another year if approved. Additionally an annually Access Review will ask users to confirm if they need the Access Package or not. If you prefer that one or more person do the access review instead of each individual user select Specific Reviewers. Administrators can create additional Access Review at anytime (discussed below).
Requesting an Access Package
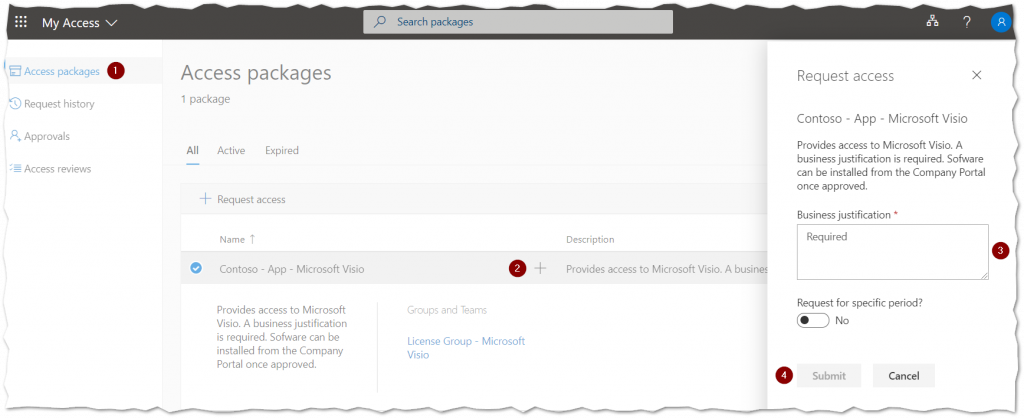
To request access an end-user simply navigates to the My Access portal – https://myaccess.microsoft.com.
- Select Access Packages from the left hand menu.
- Locate the Access Package desired and press the + button.
- Specify a Business Justification and click Submit.
The approver will now receive an email to approve or deny the users request. Status can be seen on the Request History tab.
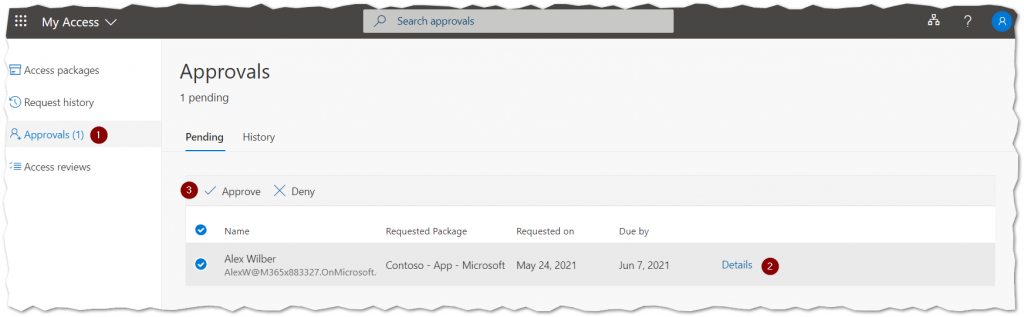
An approver navigates to the My Access portal. To view more information, such as the business justification click Details. The end-user will automatically receive an email with the approves decision.
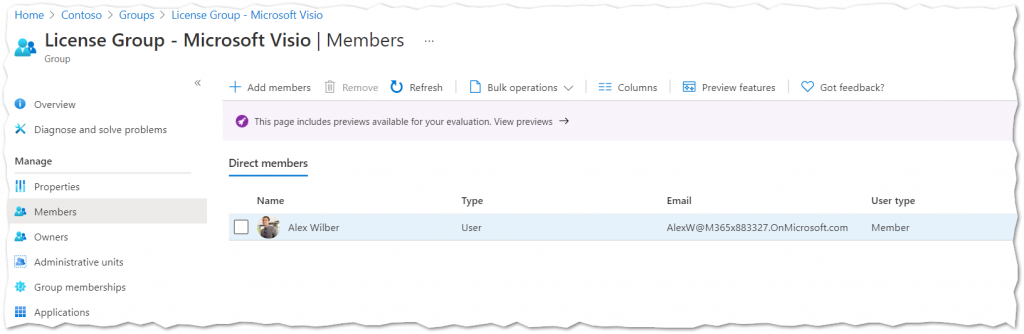
Once the Access Package is Approved, Azure AD automatically adds the user to the License Group and is provided a Microsoft Visio license. If the Visio software was deployed to the License Group using Endpoint Manager the software will also be available in Company Portal on the end-user device.
Creating an Access Reviews
Now that users have the ability to request our access package, we will create an Access Review to audit and review who has access.
- In the Azure Portal open Azure Active Directory and select the Identity Governance blade.
- Select Access Review from the left-hand side then click New Access Review.
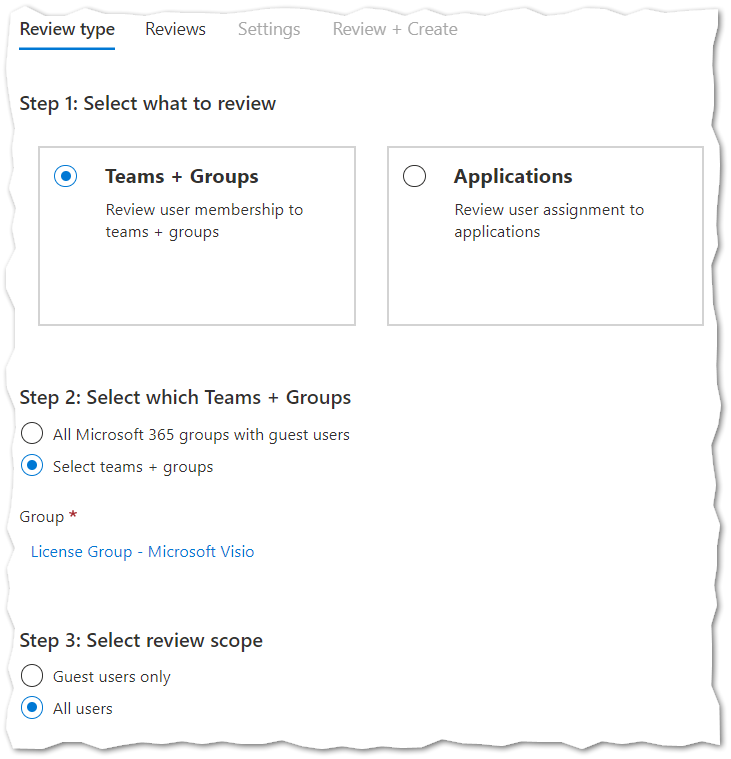
- On the Review Type page, select Teams+Groups then select the Visio licensing group.
- Under Review Scope select All Users.
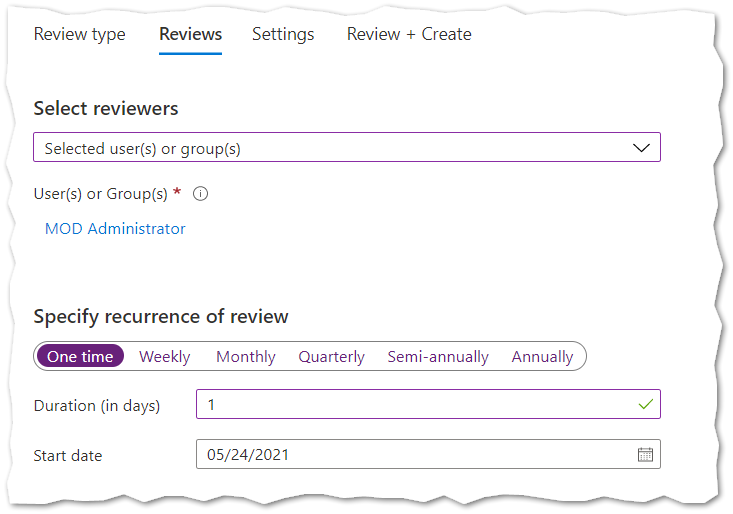
- On the Reviews page select who should review the group. Since we are simulating an administrator doing a single review we will select our administrative user and specify a one-time review. The duration can be set to a single day, but it is a good idea to increase this if someone else will be doing the review.
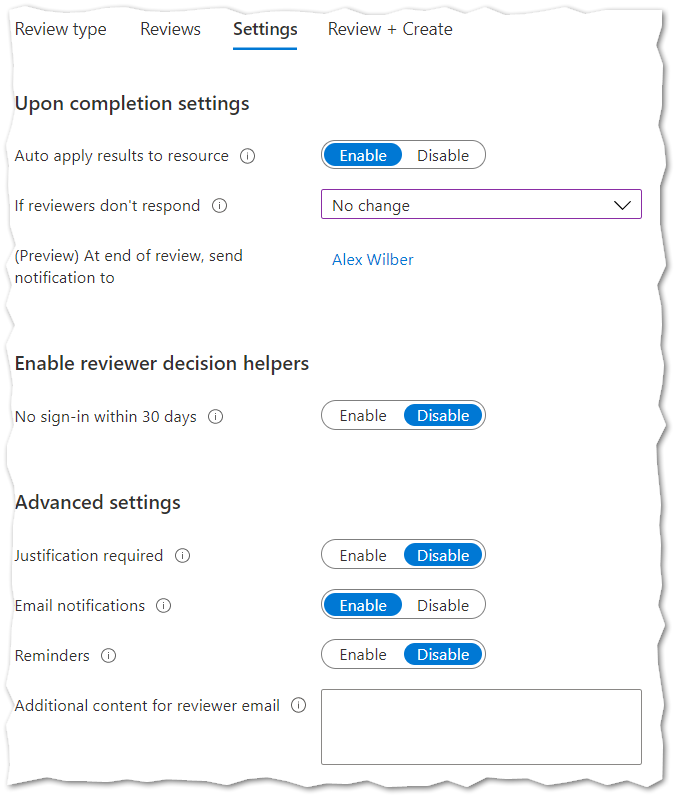
6. On the settings page there a a few things to be aware of. Adjust the settings to fit your needs and complete the wizard.
- Auto apply results to resource – If this is set to Disable users will not be removed from the Azure AD Group when the Access Review is completed.
- If reviewers dont respond – This is useful when the end-users are performing self-review. Those who do not answer within the Access Review deadline will loose access if set to Remove Access.
- Decision Helpers – If enabled the Access Review will indicate if the user has signed-in into Azure AD the last 30 days. This does not mean they have used the resource the last 30 days.
- Justification Required – If enabled the Reviewer needs to add a justification.
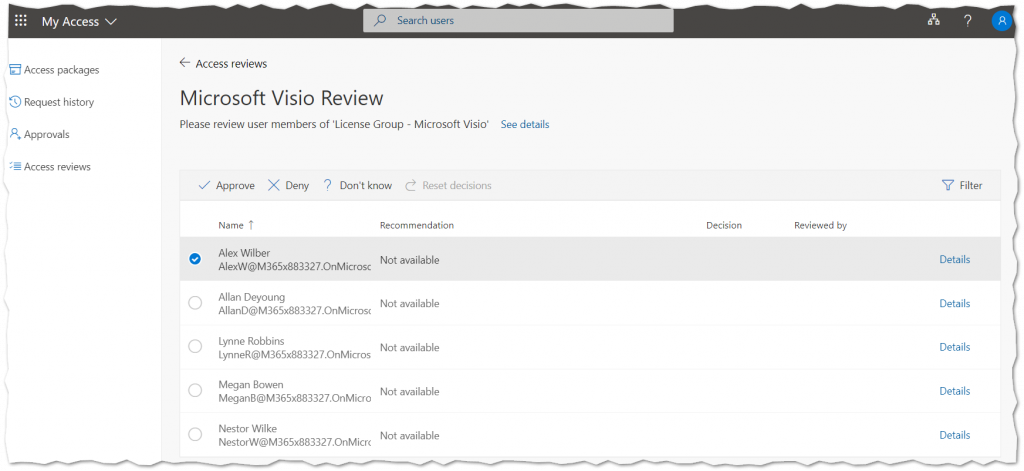
Performing an Access Review
Once an Access Review has been created, the Reviewer will be notified through e-mail with a link to the My Access portal.
- Select Access Reviews from the left hand menu.
- Select the appropriate Access Review.
- Approve or Deny users that currently have access to the resource.
Note: The access review will not automatically complete (or apply results) even if there is a response for all users. This will allow other reviewers (if any) to make any required changes within the Access Review timeframe.
Once the Access Review is completed (or manually stopped) the results will be automatically applied if the Auto apply results to resource option was enabled.