Sometimes being able to retrieve the Autopilot Hardware Hash without going through Out-Of-Box-Experience (OOBE) is really useful, especially for LAB environments. The great thing is that this is really simple to do, here are the steps. Note that the Get-WindowsAutoPilotInfo script also has an Online perimeter that can be used to directly upload the hardware hash to Intune (credentials and permissions required).
- On your admin PC download the Get-WindowsAutoPilotInfo.ps1 script by executing the PowerShell command bellow:
Save-Script -Name Get-WindowsAutoPilotInfo -Path C:\Temp
2. Open Windows PowerShell ISE (or any text editor such as Notepad) and create a PowerShell script called Register-AutoPilotDevice.ps1 that contains the following PowerShell commands:
Enable-PSRemoting -SkipNetworkProfileCheck -Force | Out-Null .\Get-WindowsAutoPilotInfo.ps1 -ComputerName $env:computername -OutputFile "$env:computername.csv"
3. Lastly create a file called Start.bat with the following contents:
@ECHO OFF powershell -ExecutionPolicy Bypass -File .\Register-AutoPilotDevice.ps1
4. Save all the files to a USB Drive and attach the USB Drive to the computer that you want to extract the AutoPilot Hardware Hash from.
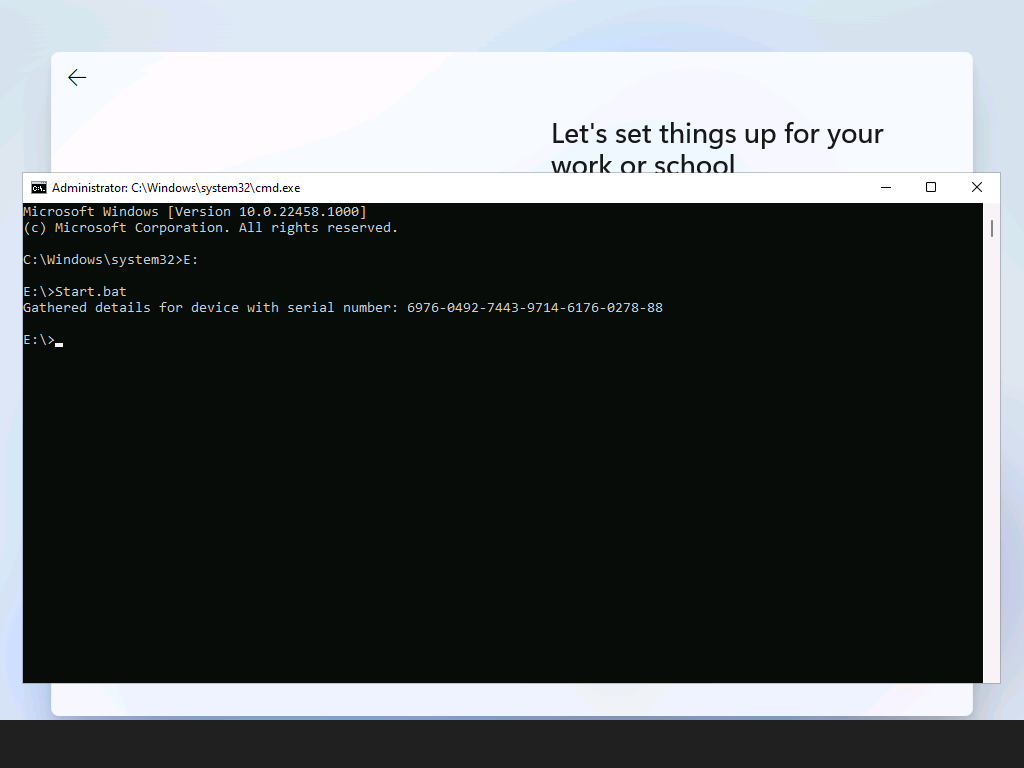
5. While in OOBE, press Shift + F10 to open a Command Prompt. Change to the USB Drive and run Start.bat.
6. A CSV file containing the AutoPilot Hardware Hash will be created on the USB Drive.
7. Upload the Hardware Hash to Intune, once the device has been assigned a profile in Intune reboot the device. The device should pickup the Autopilot profile and enroll accordingly.